If you are a WordPress user or prettend to become one and you have some IT administration knowledge this guide is of your interest. Many hostings already provide easy point and click solutions to administer WordPress over SSL. However you may be self hosting WordPress or you’re just a curious person. What is TLS? TLS […]

WordPress administration over SSL
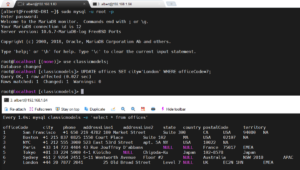
How to setup MariaDB master-slave replication on FreeBSD
Having all the data in just one server is not the best idea. Especially when talking about a database server. Spreading information in several boxes is a good measure to prevent data loss but also for performance. A MySQL/MariaDB master-slave replication scheme is often used as a good solution for both, data redundancy and speed. […]
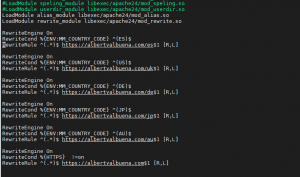
How to manage site visitors based on IP Geolocation
Whenever someone publishes a website on the internet, most of the times, their intention is that site to be seen around the globe. However, as a site administrator you may want to divert users from one country to visit some specific version of that site, maybe because of the visitor’s language. Other times, less often […]

How to setup a simple firewall in FreeBSD using IPFW
Setting the firewall up is a mandatory task on any computer facing the internet. This is a simple, straightforward how to article on how to setup a box with an easy firewall configuration on FreeBSD. If you find the articles in Adminbyaccident.com useful to you, please consider making a donation. Use this link to get […]
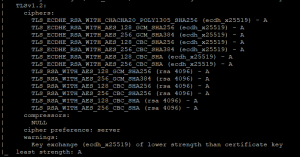
How to configure TLS 1.2 on UNIX or GNU/Linux
This is an article willing to help and point out a few useful resources for those using Apache HTTP or NGINX web servers that are still using the deprecated SSLv3, TLS 1.0 and/or TLS 1.1 verions. If you find the articles in Adminbyaccident.com useful to you, please consider making a donation. Use this link to […]
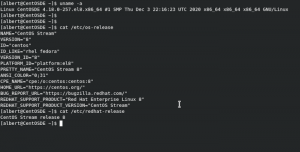
The CentOS party is over, isn’t it?
Disclaimer: What you are about to read may contain inaccuracies. Feel free to discuss them somewhere else. This is also my opinion and as such it may change through time, maybe tomorrow, next month, next year, next decade or never. I do also make very few reviews (if any) of what I write here, so […]

Abandon Linux. Move to FreeBSD or Illumos.
If you use GNU/Linux and you are only on opensource, you may be doing it wrong. Here’s why. Is your company based on opensource based software only? Do you have a bunch of developers hitting some kind of server you have installed for them to “do their thing”? Being it for economical reasons (remember to […]
What is UNIX?
UNIX is an operating system. And your known equivalent is Windows or the Mac. You may even know about Linux. The purpose of an OS is to accommodate programs in order to get some work done. Editing pictures, browsing the web or serving data from a database. It is the thing that lets you operate […]
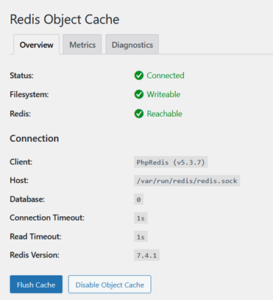
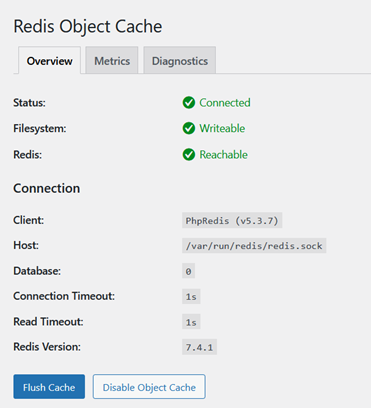
How to install Redis for WordPress on FreeBSD
I happen to self-host a few WordPress sites on FreeBSD. And as much as one can configure OP-Cache to improve PHP’s performance, object cache is a must for many WordPress sites. This how to install Redis for WordPress on FreeBSD will explain how to install an object cache (Redis) for WordPress (via plugin) on this […]
How to mitigate/solve the MDS vulnerabilities of Intel processors in FreeBSD
It had to happen again. Anyone betting on new hardware vulnerabilities on Intel processors would have won. This time these are called the MDS vulnerabilities, which stands for Microarchitectural Data Sampling. The trouble is the ones who would have really made big money would have been those stating the new CPUs were on the same […]