Nextcloud. Have you heard of it? That’s quite probable if you’re here. But, what is it, what is it? Some say it is a Google Apps replacement, some say it’s just a place to store your documents, some others just rely on it to share documents across the company and edit them just in time […]
How to install Nextcloud on FreeBSD 12
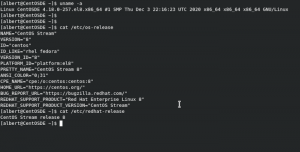
The CentOS party is over, isn’t it?
Disclaimer: What you are about to read may contain inaccuracies. Feel free to discuss them somewhere else. This is also my opinion and as such it may change through time, maybe tomorrow, next month, next year, next decade or never. I do also make very few reviews (if any) of what I write here, so […]

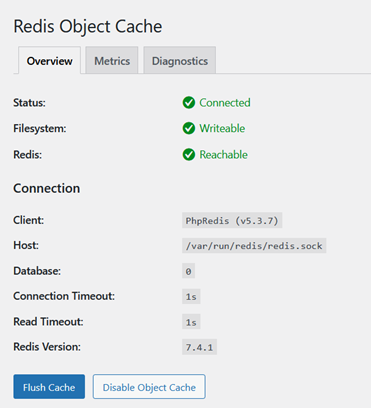
WordPress administration over SSL
If you are a WordPress user or prettend to become one and you have some IT administration knowledge this guide is of your interest. Many hostings already provide easy point and click solutions to administer WordPress over SSL. However you may be self hosting WordPress or you’re just a curious person. What is TLS? TLS […]

How to enable Geolocation in AWStats on FreeBSD 13.0
A few weeks ago, a guide explaining how to install AWStats on FreeBSD was released here in adminbyaccident.com. On that piece a basic install of AWStats is shown, however, a nice and important functionality of AWStats is missing. Knowing the location of visitors is a matter of interest, for the sake of it or because […]
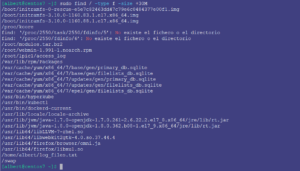
How to use find in GNU/Linux and FreeBSD
How to use find is a very basic, but important, UNIX lesson. Find is a very useful command which can help us not just finding a particular file, but for examples files or directories matching certain criteria such as: size, permissions, type. The basic mode of operation for find is the following: find path criteria […]
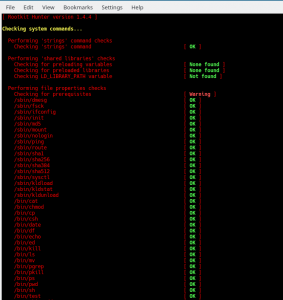
How to install RKHunter on FreeBSD
In this post you will find simple instructions to install rkhunter on FreeBSD which is a root kit “hunter” so your system/s will have some security in place for that kind of unwanted software. But for those who do not know what a rootkit is, let’s give it a simple definition (which you can get […]
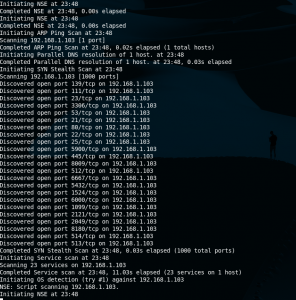
Nmap cheatsheet
Nmap is a discovery tool used in security circles but very useful for network administrators or sysadmins. One can get information about operating systems, open ports, running apps with quite good accuracy. It can even be used in substitution to vulnerability scanners such as Nessus or OpenVAS for not very large environments, or quick audits. […]

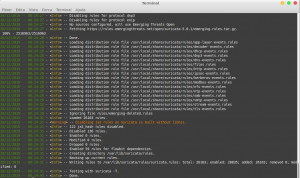
How to secure the ELK stack on CentOS 8
This is a follow up of the ‘how to install the ELK stack on CentOS 8’. That is a basic setup with no security at all. There is no encryption, no username and password setup, nothing. Not even firewall rules to filter ports. And as it’s known security can’t only rely on one factor but […]
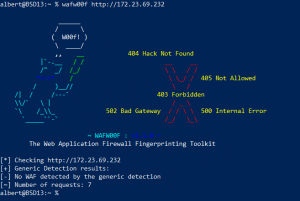
How to detect a WAF – Web Application Firewall
From a penetration testing perspective to identify if a Web Application Firewall (WAF) is in place is essential. The next question is, does an administrator need to know this? My view is, anyone who is in charge of any system that has implemented some sort of WAF needs to verify this tool is working, at […]
How to install Suricata on FreeBSD
Suricata is a free, open source, Intrusion Detection System software, or IDS for short. But it can also act as an Intrusion Prevention System, or IPS. It works by finding patterns using heuristics typically from network traffic. When configured to just warn about suspicious activity it is called an IDS, however when it blocks the […]