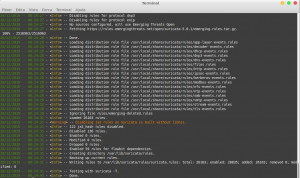
From a penetration testing perspective to identify if a Web Application Firewall (WAF) is in place is essential. The next question is, does an administrator need to know this? My view is, anyone who is in charge of any system that has implemented some sort of WAF needs to verify this tool is working, at […]
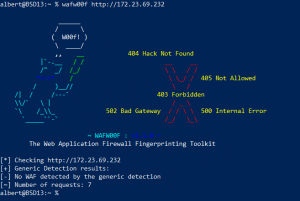
How to detect a WAF – Web Application Firewall

A word on Spectre and Meltdown
As professionals and many aficionados know, early this year some widespread vulnerabilities were found on Intel CPU’s as well as on AMD’s. It was a bit later discovered the flaws also affected some RISC architectures such as Power and ARM. Everybody went nuts and the world seemed to be tumbling because of two CPU vulnerabilities […]
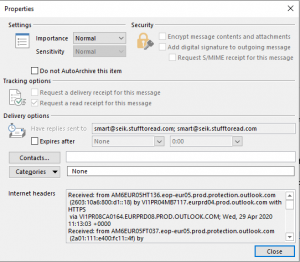
How to analyze suspicious email
Millions of emails are sent and received every day. Most of them are just junk. And many among those are potentially harmful. Phishing still is one of the most effective ways for malicious actors to penetrate into well secured networks. The weakest link, too often, is the human factor. Training can help mitigate this 24×7 […]
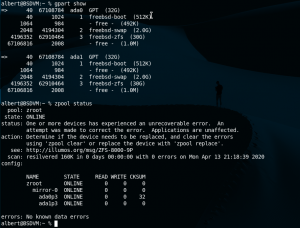
How to mirror disks on FreeBSD’s ZFS
This article is not going to be a long, detailed, specialized how to. I just wanted to share the ease and the fantastic quality of ZFS for a dead simple need I had. A spare box with a spare disk doing nothing could be repurposed as a file share box at home. Mirroring the two […]

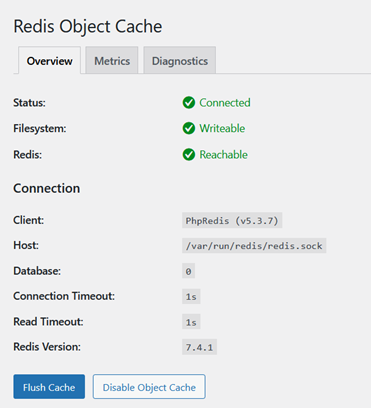
How to set Apache’s MPM Event and PHP-FPM on FreeBSD
As explained in another article the default Apache’s configuration at compile time sets its multi-processing module (MPM for short) to the pre-fork configuration setting. This is not the best performant configuration for Apache. Out of the box Apache comes compiled in its safest form, from the processing mode perspective since the pre-fork setting will open […]
How to install Suricata on FreeBSD
Suricata is a free, open source, Intrusion Detection System software, or IDS for short. But it can also act as an Intrusion Prevention System, or IPS. It works by finding patterns using heuristics typically from network traffic. When configured to just warn about suspicious activity it is called an IDS, however when it blocks the […]

Abandon Linux. Jails for developers.
Reading the title you might think I want to put developers in Jail and although some may be good candidates this is in the far opposite of my intention. I am talking about FreeBSD Jails. For the unfamiliar with the concept those Jails are userland secure contained environments that share a common kernel. Purists and […]

FreeBSD Jails
The FreeBSD jails is a virtualization technology you may have skipped for too long. It is an operating system level virtualization and is one of the differential characteristics of FreeBSD from Linux. Solaris took it to the main corporate use with Zones and as it couldn’t be any other way the Illumos folks also play […]

How to install AWStats on FreeBSD 13.0
AWStats is a very powerful and useful software allowing webmasters count the visits to their managed websites. The tool is basically coded in Perl and it was a very popular choice before Google made it way easy when they launched their Google Analytics tool. However, nowadays not everyone is using Google Analytics services and even […]
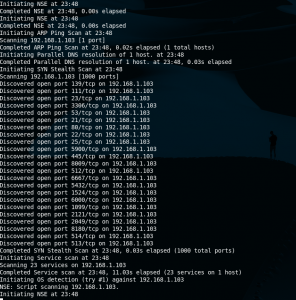
Nmap cheatsheet
Nmap is a discovery tool used in security circles but very useful for network administrators or sysadmins. One can get information about operating systems, open ports, running apps with quite good accuracy. It can even be used in substitution to vulnerability scanners such as Nessus or OpenVAS for not very large environments, or quick audits. […]