I am a busy guy. Answering comments takes precious time from my daily life so don’t get mad if I don’t reply you back quickly or if I just don’t do. Plus, think twice before posting. If you really have something interesting to say, just go ahead. If that is something you really think I’d […]
Contact

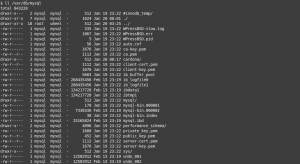
How to install Apache in FreeBSD with pkgng
The Apache Web Server is one of the most widely deployed web servers around the world. There are new and powerful alternatives you may have heard of, such as NGINX which seems to be the coolest thing around lately. There are meaningful differences between the two. Both are great but for example Apache has set […]
What is Expect?
Expect is a handy scripting tool for task automation. You may have never heard of it. I heard about many scripting things before. But one day I needed something simple but didn’t know how to proceed, what would be a good tool for my purpose. The task was simple. Exporting a website content from a […]

How to install Nessus 10 on FreeBSD 12
Nessus is a professional vulnerability scanner from the reputable cybersecurity company Tenable. I have already written about it in the past but installing it on a GNU/Linux distro. This very article will guide anyone to install Nessus 10 on FreeBSD, since Tenable is releasing binaries for FreeBSD 11 and 12 as of the time of […]
A brief introduction to Regular Expressions
A regular expression is a set of characters, a string of characters if you will, that specify a pattern. Ever used the grep command? It makes use of them. The ‘grep’ command is very handful when one needs to look for certain things inside a text file, or looking for some specific pattern from another […]
How to install the ELK stack on CentOS 8
The ELK stack stands for Elasticsearch, Logstash and Kibana. These three pieces of software are very useful since each brings a powerful capability that in combination is just great to use. Elasticsearch is a search and analytics engine. Logstash can process data from multiple sources. Kibana allows to visualize data in a graphic manner. These […]
How to upgrade MariaDB on FreeBSD
As we all know a best practice recommendation that has been made forever, and forever many are just skipping, is running up to date software and it is one of the core fundamentals of IT. If you happen to use MariaDB on FreeBSD, the official guide on their website may not be that all helpful […]
The firewall
If you don’t know why you need a firewall it’s because you are not very tech savy. Don’t worry. You can discover by yourself why you need one. The router sitting in your house has one installed in it. And please don’t disable that by any mean. You can check why a firewall is important […]
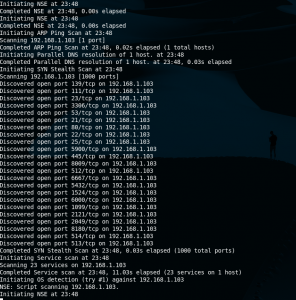
Nmap cheatsheet
Nmap is a discovery tool used in security circles but very useful for network administrators or sysadmins. One can get information about operating systems, open ports, running apps with quite good accuracy. It can even be used in substitution to vulnerability scanners such as Nessus or OpenVAS for not very large environments, or quick audits. […]
How to install Docker on Ubuntu 18.04
Operating System level virtualization is hitting hard now, as much as VM’s did just a few years ago. Docker is the popular framework for this matter, the new kid on the block so to speak. This is the hot spot now and if anyone wants to appear knowledgeable about system administration knowing this technology is […]